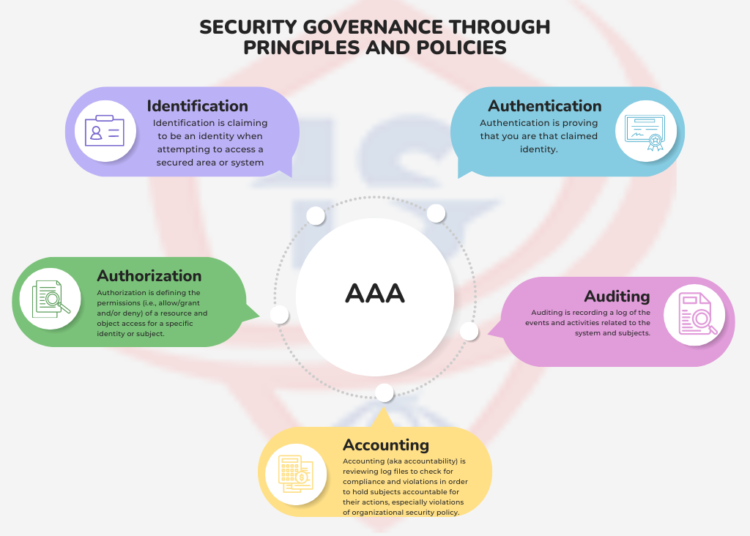
The five core elements of security—Identification, Authentication, Authorization, Auditing, and Accountability (AAA)—represent the processes that ensure the secure access and operation of a system. These processes are vital to the integrity and functionality of any security system.
Identification
Identification is the act of claiming an identity when attempting to access a secured system or area. This can involve typing a username, swiping a smartcard, or using biometric data such as a fingerprint or facial recognition. Identification is the first step in the AAA process and is essential for associating a subject with an identity.
Once an identity is recognized and verified, the system tracks activities associated with that identity, not with the subject directly. The system distinguishes users by their unique user accounts, and simply claiming an identity does not grant access; that identity must first be proven through authentication.
Authentication
Authentication is the process of verifying that a claimed identity is valid. The most common form of authentication is through passwords, where additional information is required to prove the subject’s identity. Authentication is crucial in determining if the provided identity corresponds to a valid user account in the system.
Identification and authentication often occur together in a two-step process: first, the subject provides an identity, and second, they provide authentication factors (e.g., passwords). Without both, a subject cannot access the system.
Each authentication method has its unique strengths and weaknesses, and their viability should be evaluated based on the environment in which they are deployed.
Authorization
Once a subject is authenticated, they still require authorization to access resources. Authorization determines whether the authenticated subject has the appropriate permissions to perform the requested actions or access certain objects.
Authorization works by evaluating the subject’s identity, the requested object, and the assigned permissions. A subject may have limited permissions—such as reading a file but not editing it or printing a document but not altering the print queue.
Auditing
Auditing involves recording a log of activities and actions taken by subjects in the system. It helps detect unauthorized or abnormal actions and provides a record that can be used for investigations, reconstructions, and accountability.
Auditing generates an audit trail that tracks subjects’ activities and can be used as evidence during legal proceedings, making it crucial for detecting malicious activities, intrusions, or system failures. Monitoring is often part of auditing, though they are distinct activities—monitoring involves real-time oversight, while auditing records activities for future analysis.
Accountability
Accountability ensures that subjects are held responsible for their actions. It ties the identity of a subject to their actions within a system. Accountability relies on effective identification, authentication, authorization, and auditing processes. Without strong authentication methods, it becomes difficult to hold a subject accountable for any malicious or unauthorized actions.
In a legal context, accountability must be defensible. For example, if only passwords are used for authentication, it may be difficult to prove beyond doubt that the person associated with a user account was the one responsible for an action. However, multifactor authentication—such as a combination of a password, smartcard, and biometric verification—provides stronger evidence that the authenticated subject is indeed accountable for their actions.